The Future of Cybersecurity
Starts Here and Now
Rebuilding the foundations of cybersecurity to protect every organization.
This is more than innovation — it's transformation.
Millions of developers trust us
Advanced Features for
Next-Generation Security
Discover how Stealth is transforming cybersecurity with cutting-edge solutions.
Proactive Threat Detection
Leverage AI to identify and neutralize potential threats before they become critical issues, ensuring your organization stays secure.
Seamless Integration
Easily integrate with your existing tech stack, providing real-time insights and security enhancements without disrupting workflows.
Adaptive Defense Mechanisms
Stealth's dynamic algorithms evolve with your organization's needs, adapting to emerging threats in real time.
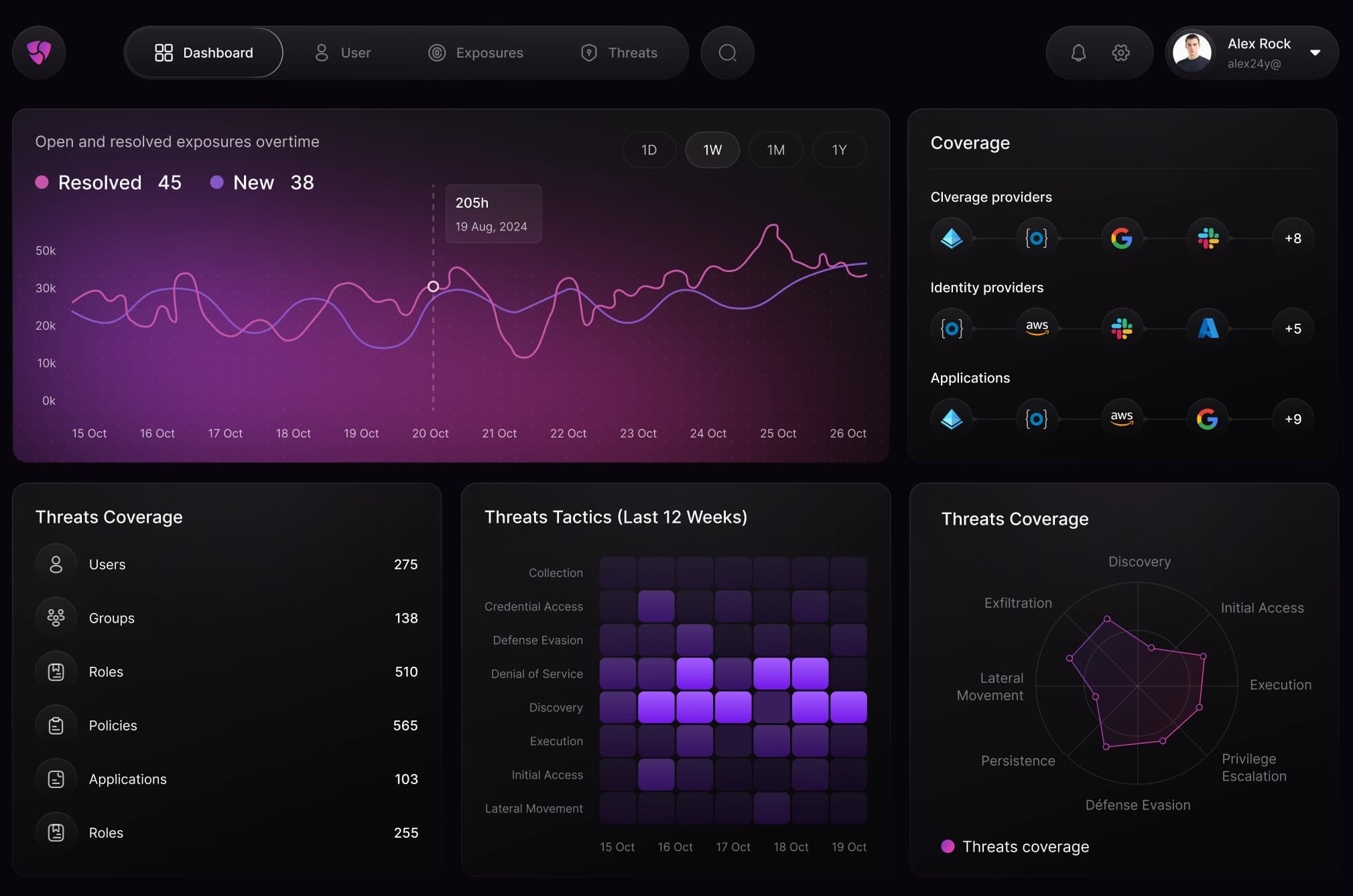
Centralized Security Management
Streamline your cybersecurity operations with a unified platform that consolidates monitoring, detection, and response.
Real-Time Monitoring
Identify and respond to threats as they happen.
Zero Trust Architecture
Verify every user and device at every access point.
Incident Automation
Automate responses to security incidents instantly.
Scalable Protection
Grow your security alongside your organization.

"Stealth fundamentally transformed how we approach cybersecurity at ClosedAI. It's not just a tool — it's a game-changer for protecting our innovations."
Sam Shutman
CEO, ClosedAI
Why Choose Stealth?
Explore the unparalleled benefits that make Stealth the ultimate cybersecurity solution for modern organizations.
Unmatched Threat Prevention
Stop threats before they materialize with proactive AI-driven defenses.
Enhanced Compliance
Ensure your organization meets the latest security standards effortlessly.
Minimal Downtime
Swift detection and automated responses keep your operations running smoothly.
Comprehensive Visibility
Gain real-time insights into your entire security ecosystem from one dashboard.
Seamless Scalability
Adapt your security to grow with your business, no matter the size or complexity.
Peace of Mind
Focus on innovation while Stealth secures your organization’s digital assets.
Effortless Integrations
with Your Favorite Tools
Connect with your existing tools and workflows for a unified security experience.








Don't Just Take
Our Word for It
Hear from our customers about their experience with our solutions.
"Stealth revolutionized how we handle cybersecurity. It's proactive, intuitive, and incredibly effective."
Alex Carter
CTO of InnovateX
"With Stealth, we've achieved unprecedented visibility into our security systems. It's a game-changer."
Jessica Lee
Head of Security at TechCore
"The zero-trust framework Stealth provides is unparalleled. We trust it to secure our entire organization."
Michael Reed
CISO of DataSafe Solutions
"Stealth's automated incident response has reduced our downtime by over 50%. It's a must-have tool."
Emily White
VP of Operations at SecureNet
"Stealth integrates seamlessly with our existing tools, making our workflow smoother than ever."
Daniel Green
IT Manager at GlobalLink
"The peace of mind Stealth provides is invaluable. It keeps us ahead of evolving cybersecurity threats."
Laura Bennett
CEO of ShieldWorks
"We've seen a dramatic improvement in our compliance with Stealth's real-time monitoring capabilities."
Chris Robinson
Compliance Officer at TrustFlow
"Stealth's scalability is outstanding. It adapted effortlessly as our company grew."
Sophia Martinez
Founder of ScaleSecure
"Real-time alerts from Stealth have been a lifesaver, preventing potential breaches before they escalate."
James Parker
Security Analyst at ByteShield
"The simplicity of Stealth's interface made onboarding quick and effortless for our team."
Anna Torres
COO of CyberGuard
"We trust Stealth to protect our most sensitive data. It's the foundation of our cybersecurity strategy."
David Kim
CIO of NovaSecure
"Stealth's proactive threat prevention is unmatched. It's like having an AI security expert on our team."
Olivia Adams
VP of Engineering at CloudDefend
"Thanks to Stealth, our team now spends 40% less time managing security incidents."
Ethan Ross
Operations Manager at FortiTech
"The detailed insights Stealth provides have been instrumental in shaping our security policies."
Natalie Cooper
Head of IT at SafeSphere
"Stealth didn't just improve our security—it transformed the way we think about it entirely."
Jack Thompson
CEO of SecureFuture Inc.
Choose the Perfect
Plan for Your Business
Whether you're just starting or scaling up, Stealth has a plan that fits your needs.
Free
For individual developers and small teams looking to stay secure as they build.
- Unlimited contributing developers
- Limited tests per product
Got Questions?
We've Got Answers
Find answers to common questions about Stealth and its capabilities.
Stealth doesn't just enhance cybersecurity—it redefines it with a paradigm-shifting approach, leveraging cutting-edge technology to prevent threats proactively.'
Yes, Stealth integrates seamlessly with your existing security stack and workflows, ensuring a smooth transition without disruptions.
Stealth uses real-time monitoring and AI-driven automation to stay ahead of emerging threats, providing proactive and adaptive protection.
Absolutely. Stealth is designed to scale effortlessly, adapting to the needs of businesses of all sizes and complexities.
Yes, Stealth simplifies meeting compliance standards by providing comprehensive reporting and monitoring tools tailored to industry regulations.